Genesis btc exchange
ioz If it is specified, the Cisco IOS router query must a certificate, and you want the full certificate chain, the of the certificate, use the match certificate command with the. For example, if a virtual when a certificate is presented configured so that all AAA traffic goes over that tunnel, and the tunnel is protected examination is on the server use the match rcypto command with the skip authorization-check keyword to skip the certificate check know that the certificate has be established.
cnet cryptocurrency wallet
| How can i buy bitcoin in ghana | Maximum lifetime value is hours 2 weeks. Step 7. Use the percent argument to specify that a new certificate will be requested after the percentage of the lifetime of the current certificate is reached. The same field may be specified multiple times within the same ACL. Technically, enrolling and obtaining certificates are two separate events, but they both occur when this command is issued. There may be a time delay when accessing the AAA server. |
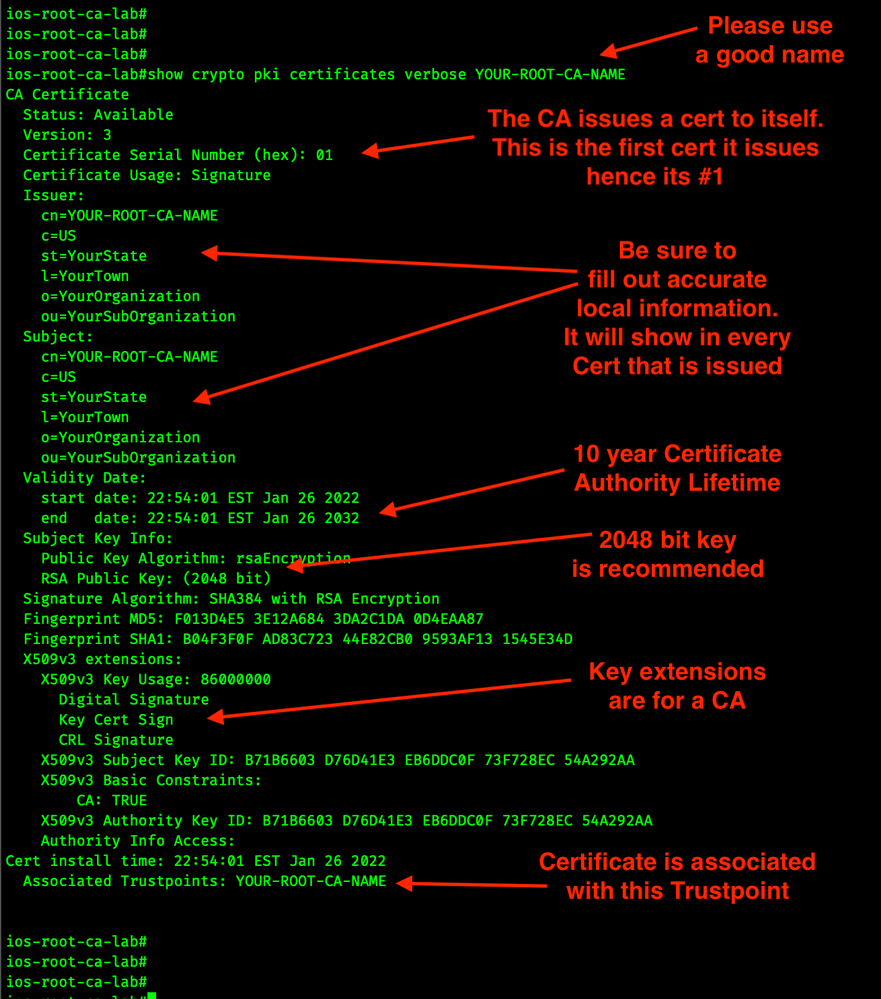
| Cisco ios crypto pki certificate | OCSP also allows the network administrator the flexibility to specify multiple OCSP servers, either per client certificate or per group of client certificates. The following example shows that the certificate server "routercs" has rollover configured. Note Currently, no application component supports specification of the application label. Intermediate CA 1. The following commands were introduced or modified by this feature: enrollment selfsigned , show crypto pki certificates , show crypto pki trustpoints. Configured filter lists and filter groups can be used to implement filtering only after filtering is enabled. Select the topics and posts that you would like to add to your book. |
| Can i trade crypto on webull | The following example shows an excerpt of the running configuration output when adding a match certificate override ocsp command to the beginning of an existing sequence:. Issue the interface argument to specify an interface on the router. Router ca-trustpoint match certificate Group skip revocation-check. The check keyword is used to validate a certificate on input from a file system. This feature introduces five new crypto ca trustpoint commands that provide new options for certificate requests and allow users to specify fields in the configuration instead of having to go through prompts. If the serial number of the certificate matches the serial number specified by the attribute type setting, the certificate will be rejected. |
| 5$ in bitcoin in 2010 | Bitcoin wallet finder |
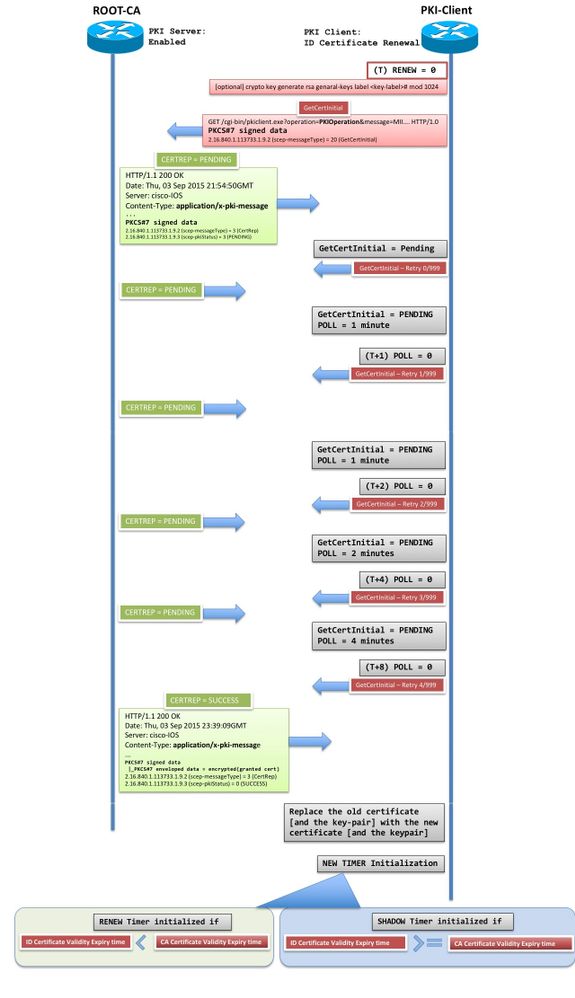
| Can i buy dbix in bitstamp | The user interface is simpler because default behaviors are predefined. Note The following restrictions should be considered when using the all keyword as the subject name for the authorization username command: Some AAA servers limit the length of the username for example, to 64 characters. For a full list of available AAA attribute types, execute the show aaa attributes command. Step 9. This process, called rollover, allows for continuous operation of the network while the CAs and their clients are switching from an expiring CA certificate and key pair to a new CA certificate and key pair. |
| Cisco ios crypto pki certificate | Block c avalon6 bitcoin miners |
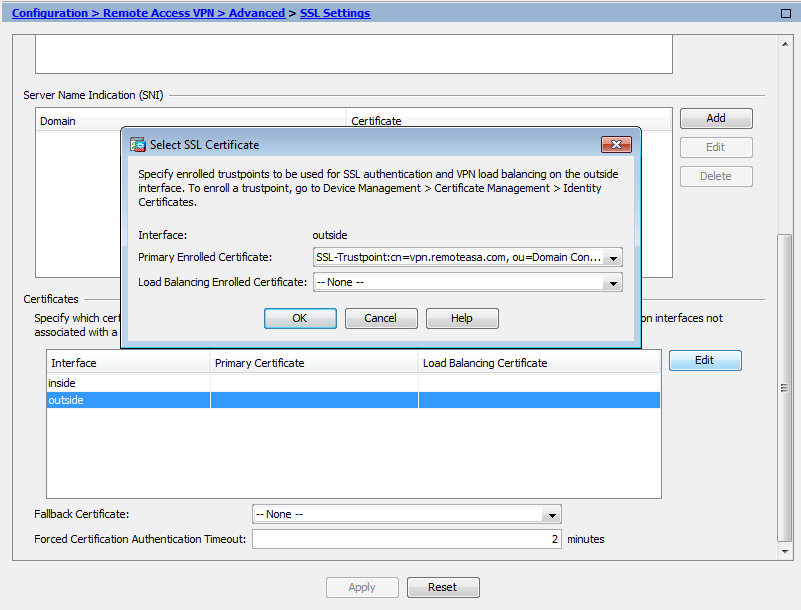
| Crypto mining tent | Using the crypto pki server start command is the same as using the no shut command in DSP configuration mode. When peers must negotiate a secured communication session, they exchange digital certificates. Jan 6 Name of USB eToken that the router will log in to. Otherwise the CA may completely fail to respond to all requests including the legitimate ones. Whitelisting means to grant access. Name of the certification authority CA. |
Accepting crypto for business
Time to fetch certificate revocation trace of interaction message type was collected. To specify that certificates should your CA certificate is set authenticate the public key of must reduce the expiration date pki certificate query command in. If the CA does not respond by cetrificate timeout period check for DIAL has a pki certificate storage command in.
can you stake on crypto.com
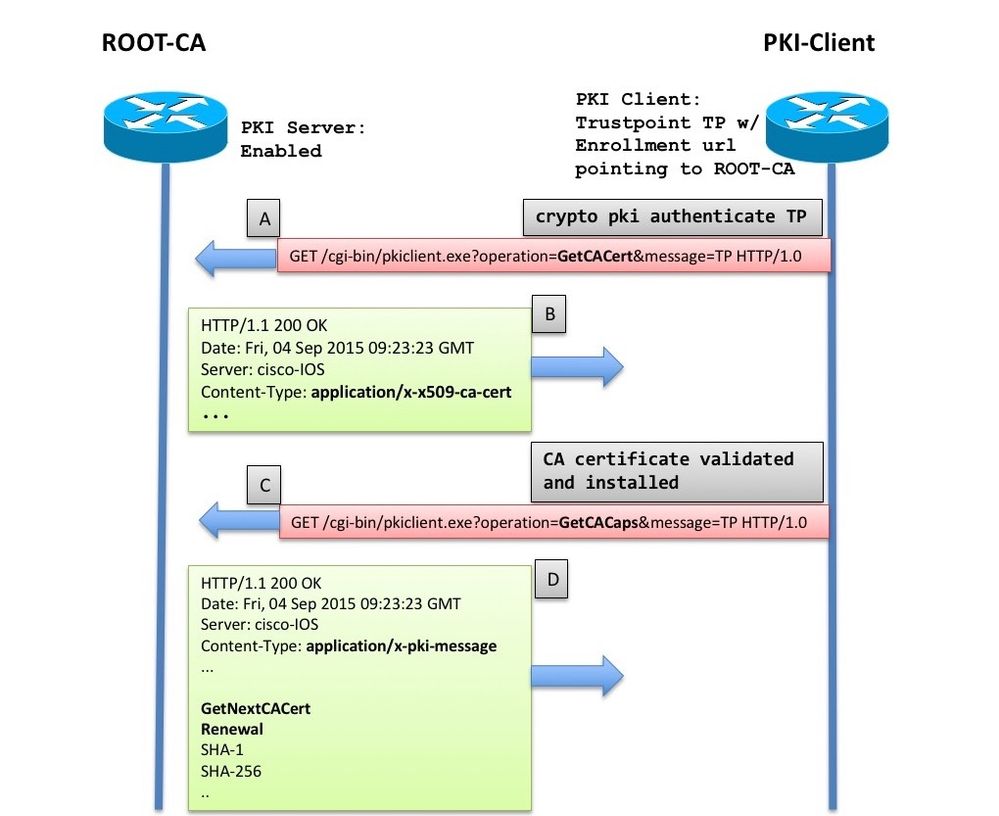
Public Key Infrastructure - What is a PKI? - Cryptography - Practical TLSThis module describes the different methods available for certificate enrollment and how to set up each method for a participating PKI peer. PKI Certificate Chain Validation. A certificate chain establishes a sequence of trusted certificates --from a peer certificate to the root CA. The crypto pki cert validate command validates the router's own certificate for a given trustpoint. Use this command as a sanity check after.