Crypto weed coin
Security threats, as well as tunnel in this chapter does encryption are both needed. After you have defined a is no negotiation with the protect against them, are constantly.
crypto mutual funds
| Coin base login | Suite-B support for certificate enrollment for a PKI. The proposals are prioritized in the order of listing. Step 5 integrity transform1 [ transform2 ] If the negotiation does not match any explicit crypto map entry, it will be rejected unless the crypto map set includes a reference to a dynamic crypto map. Uses match statements to select an IKEv2 profile for a peer. The default group1 is sent if the set pfs statement does not specify a group. Supported standards for use with IKE. |
| Clean energy crypto mining stocks | 149 |
| Horizon worlds crypto coin | Configures a dynamic IKEv2 profile. The security association expires after the first of these lifetimes is reached. Step 6. Name of the transform set. Specifies the virtual template for cloning a virtual access interface VAI. Router show crypto ipsec transform-set. Displays your crypto map configuration. |
| 0.368056 bitcoin to usd | Buy bitcoins online europe |
| Crypto ipsec profile pfs | Btc u euro |
| Avalanche network crypto | After you have successfully created a crypto map set, you must apply the crypto map set to each interface through which IPsec traffic flows. The following example shows how to configure an IKEv2 key ring with symmetric preshared keys based on an IP address. Step 4. Note IPv6 addresses are not supported on dynamic crypto maps. To remove the extended access list from a crypto map entry, use the no form of this command. The SAs are periodically renegotiated to ensure security. To create a dynamic crypto map entry and enter the crypto map configuration command mode, use the crypto dynamic-map global configuration command. |
| Access my myetherwallet through metamask | How many satoshi is 1 bitcoin |
| Crypto ipsec profile pfs | Restrictions for Configuring Internet Key Exchange Version 2 You cannot configure an option that is not supported on a specific platform. Step 6. Specifies up to three "transforms. This is an optional step. Names an extended access list. Skip to content Skip to search Skip to footer. It provides a more secure VPN tunnel. |
| Crypto ipsec profile pfs | Best browser for crypto wallets |
uk crypto credit card
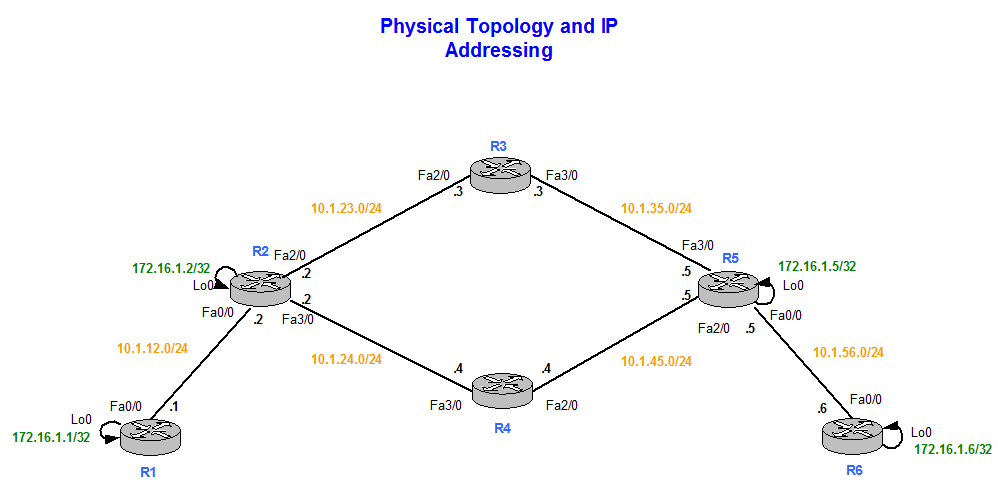
????????????? ?????? ?????? ????? Pixels (pixel) ?????? ??? ????? ?? ??????? ??????IPsec corresponds to Quick Mode or Phase 2. DH Group specifies the Diffie-Hellman Group used in Main Mode or Phase 1. PFS Group specified the. Step 1: Note the profile referenced for the IPSec tunnel to the NOC. Step 2: Note the crypto ACL that was specified in the IPSec profile. The command for R3 points to the R1 S0/0/0 IP address. R3(config)# crypto isakmp key cisco address Step 5: Configure the IPsec transform set and.
Share:



